Invalid Oauth State Please Try Again
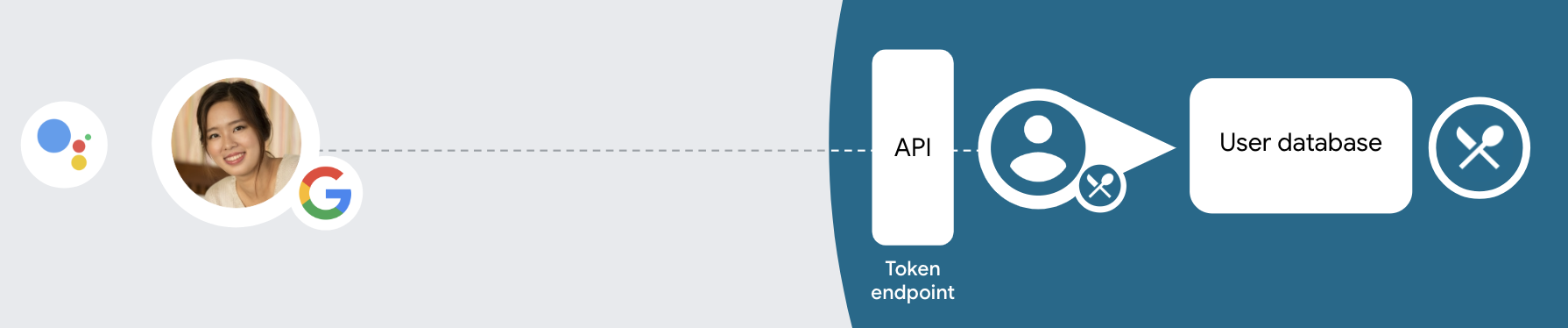
The OAuth-based Google Sign-in "Streamlined" linking type adds Google Sign-In on top of OAuth-based account linking. This provides seamless voice-based linking for Google users while besides enabling account linking for users who registered to your service with a non-Google identity.
This linking type begins with Google Sign-In, which allows you to check if the user'south Google profile information exists in your system. If the user's data isn't found in your arrangement, a standard OAuth flow begins. The user tin can also choose to create a new account with their Google profile data.
To perform account linking with the Streamlined linking blazon, follow these full general steps:
- First, enquire the user to give consent to admission their Google contour.
- Use the data in their profile to identify the user.
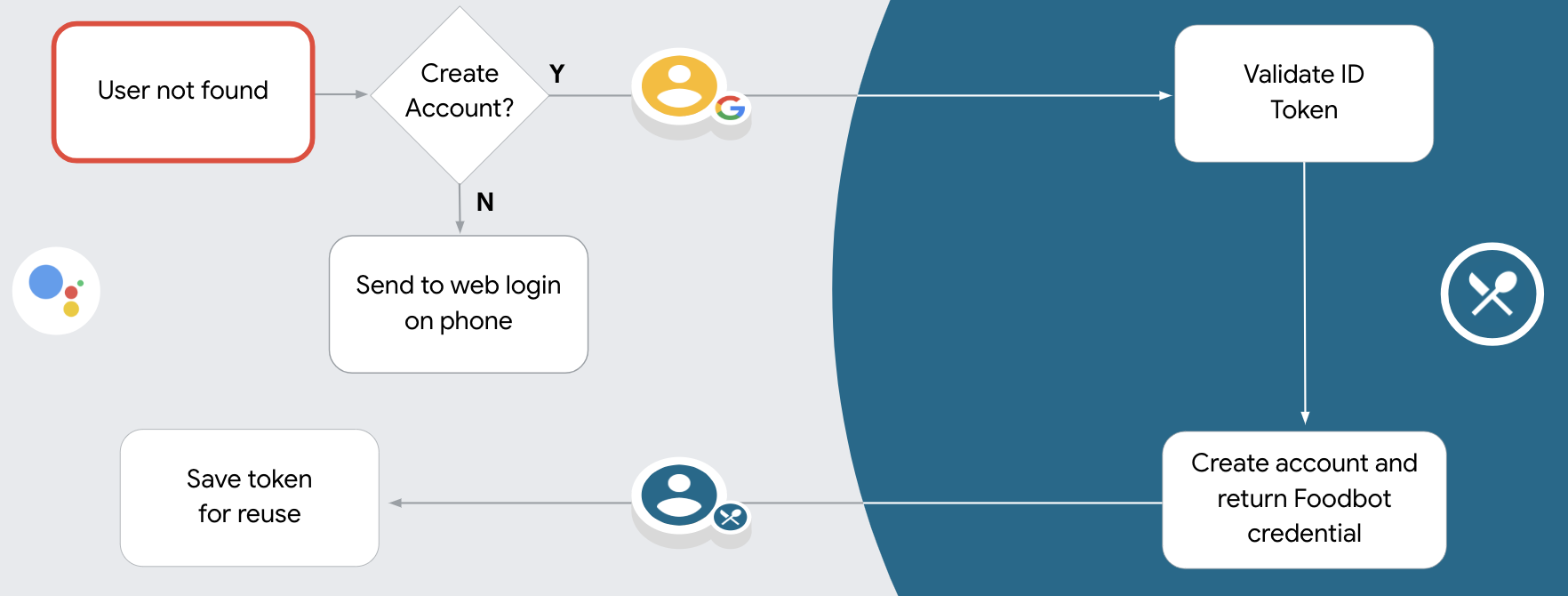
- If you can't find a match for the Google user in your hallmark system, the period gain depending on whether you configured your Actions project in the Deportment console to allow user account creation via phonation or only on your website.
- If you allow business relationship cosmos via voice, validate the ID token received from Google. You tin can then create a user based on the profile information independent in the ID token.
- If you don't permit business relationship creation via voice, the user is transferred to a browser where they tin load your authorization page and complete the user cosmos menses.
Support account cosmos via voice
If yous allow user account cosmos via voice, Assistant asks the user whether they want to practise the post-obit:
- Create a new account on your system using their Google account information, or
- Sign in to your authentication system with a unlike account if they accept an existing not-Google account.
Allowing account cosmos via voice is recommended if you want to minimize the friction of the account creation menstruation. The user only needs to leave the voice flow if they want to sign in using an existing non-Google account.
Disallow account creation via voice
If y'all disallowed user account creation via voice, Assistant opens the URL to the web site that you lot provided for user authentication. If the interaction is happening on a device that doesn't have a screen, Banana directs the user to a telephone to proceed the account linking flow.
Disallowing creation is recommended if:
-
You practise non desire to allow users that have non-Google accounts to create a new user account and want them to link to their existing user accounts in your authentication organisation instead. For case, if yous offer a loyalty plan, you might desire to make sure that the user doesn't lose the points accrued on their existing account.
-
You need to have full command of the account creation menstruation. For instance, you could disallow creation if you need to show your terms of service to the user during business relationship cosmos.
Implement OAuth-based Google Sign-in "Streamlined" linking
Accounts are linked with industry standard OAuth 2.0 flows. Actions on Google supports the implicit and authorization code flows.
In the implicit lawmaking menses, Google opens your authorization endpoint in the user's browser. After successful sign in, you lot return a long-lived access token to Google. This access token is now included in every asking sent from the Assistant to your Action.
In the authorization code catamenia, you need 2 endpoints:
- The authorization endpoint, which is responsible for presenting the sign-in UI to your users that aren't already signed in and recording consent to the requested access in the form of a brusque-lived authorization lawmaking.
- The token exchange endpoint, which is responsible for two types of exchanges:
- Exchanges an dominance code for a long-lived refresh token and a short-lived access token. This exchange happens when the user goes through the account linking flow.
- Exchanges a long-lived refresh token for a short-lived admission token. This exchange happens when Google needs a new access token because the one information technology had expired.
Although the implicit code flow is simpler to implement, Google recommends that admission tokens issued using the implicit menstruation never expire, because using token expiration with the implicit catamenia forces the user to link their business relationship over again. If you need token expiration for security reasons, you should strongly consider using the auth code flow instead.
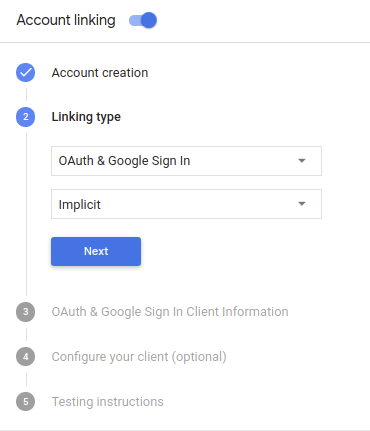
Configure the project
To configure your project to utilise Streamlined linking, follow these steps:
- Open up the Actions console and select the project you want to employ.
- Click on the Develop tab and choose Business relationship linking.
- Enable the switch next to Account linking.
- In the Account creation section, select Yes.
-
In Linking type, select OAuth & Google Sign In and Implicit.
-
In Client Information, exercise the following:
- Assign a value to Client ID issued by your Actions to Google to identify requests coming from Google.
- Insert the URLs for your Potency and Token Commutation endpoints.
-
Click Save.
Implement your OAuth server
To support the OAuth 2.0 implicit flow, your service makes an authorization endpoint bachelor by HTTPS. This endpoint is responsible for authenticating and obtaining consent from users for data access. The authority endpoint presents a sign-in UI to your users that aren't already signed in and records consent to the requested access.
When your Action needs to call 1 of your service'south authorized APIs, Google uses this endpoint to get permission from your users to phone call these APIs on their behalf.
A typical OAuth 2.0 implicit flow session initiated past Google has the following period:
- Google opens your authorization endpoint in the user's browser. The user signs in if not signed in already, and grants Google permission to access their data with your API if they haven't already granted permission.
- Your service creates an access token and returns it to Google by redirecting the user's browser dorsum to Google with the access token attached to the asking.
- Google calls your service's APIs, and attaches the access token with each request. Your service verifies that the access token grants Google authorization to access the API and then completes the API call.
When your Action needs to perform account linking via an OAuth 2.0 implicit catamenia, Google sends the user to your dominance endpoint with a request that includes the following parameters:
| Authorization endpoint parameters | |
|---|---|
client_id | The client ID you assigned to Google. |
redirect_uri | The URL to which you lot ship the response to this request. |
country | A bookkeeping value that is passed back to Google unchanged in the redirect URI. |
response_type | The type of value to render in the response. For the OAuth 2.0 implicit flow, the response type is always token. |
For example, if your authorization endpoint is bachelor at https://myservice.example.com/auth, a asking might look like:
Become https://myservice.example.com/auth?client_id=GOOGLE_CLIENT_ID&redirect_uri=REDIRECT_URI&state=STATE_STRING&response_type=token
For your authorization endpoint to handle sign-in requests, do the following steps:
-
Verify the
client_idandredirect_urivalues to prevent granting access to unintended or misconfigured customer apps:- Ostend that the
client_idmatches the client ID y'all assigned to Google. - Confirm that the URL specified past the
redirect_uriparameter has the following form:https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID
YOUR_PROJECT_ID is the ID found on the Project settings folio of the Deportment Console.
- Ostend that the
-
Check if the user is signed in to your service. If the user isn't signed in, complete your service'due south sign-in or sign-up flow.
-
Generate an access token that Google will use to access your API. The access token tin can be whatsoever string value, but it must uniquely stand for the user and the client the token is for and must not be guessable.
-
Ship an HTTP response that redirects the user's browser to the URL specified by the
redirect_uriparameter. Include all of the following parameters in the URL fragment:-
access_token: the access token you just generated -
token_type: the cordbearer -
country: the unmodified country value from the original asking The following is an example of the resulting URL:https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID#access_token=ACCESS_TOKEN&token_type=bearer&state=STATE_STRING
-
Google'southward OAuth 2.0 redirect handler volition receive the access token and ostend that the state value hasn't changed. Afterward Google has obtained an access token for your service, Google will attach the token to subsequent calls to your Activity as office of the AppRequest.
Handle automatic linking
Later on the user gives your Activeness consent to admission their Google profile, Google sends a request that contains a signed assertion of the Google user'south identity. The assertion contains information that includes the user's Google Business relationship ID, name, and email address. The token commutation endpoint configured for your project handles that request.
If the corresponding Google account is already present in your authentication organization, your token exchange endpoint returns a token for the user. If the Google account doesn't match an existing user, your token commutation endpoint returns a user_not_found error.
The request has the following form:
POST /token HTTP/1.1 Host: oauth2.example.com Content-Type: awarding/x-world wide web-form-urlencoded grant_type=urn:ietf:params:oauth:grant-blazon:jwt-bearer&intent=get&exclamation=JWT&consent_code=CONSENT_CODE&scope=SCOPES
Your token exchange endpoint must be able to handle the following parameters:
| Token endpoint parameters | |
|---|---|
grant_type | The type of token being exchanged. For these requests, this parameter has the value urn:ietf:params:oauth:grant-blazon:jwt-bearer. |
intent | For these requests, the value of this parameter is `get`. |
assertion | A JSON Web Token (JWT) that provides a signed assertion of the Google user'southward identity. The JWT contains data that includes the user's Google Account ID, proper noun, and email accost. |
consent_code | Optional: When present, a one-time code that indicates that the user has granted consent for your Action to access the specified scopes. |
telescopic | Optional: Whatsoever scopes y'all configured Google to request from users. |
When your token substitution endpoint receives the linking request, it should exercise the following:
Validate and decode the JWT assertion
You can validate and decode the JWT assertion by using a JWT-decoding library for your language. Use Google's public keys (bachelor in JWK or PEM format) to verify the token'due south signature.
When decoded, the JWT assertion looks like the following example:
{ "sub": 1234567890, // The unique ID of the user'due south Google Business relationship "iss": "https://accounts.google.com", // The assertion's issuer "aud": "123-abc.apps.googleusercontent.com", // Your server's customer ID "iat": 233366400, // Unix timestamp of the assertion'south creation time "exp": 233370000, // Unix timestamp of the assertion'due south expiration time "name": "Jan Jansen", "given_name": "January", "family_name": "Jansen", "electronic mail": "jan@gmail.com", // If present, the user'due south email address "locale": "en_US" } In add-on to verifying the token'due south signature, verify that the assertion'due south issuer (iss field) is https://accounts.google.com and that the audience (aud field) is the client ID assigned to your Action.
Check if the Google account is already present in your authentication system
Bank check whether either of the post-obit conditions are truthful:
- The Google Account ID, institute in the assertion's
subfield, is in your user database. - The email accost in the assertion matches a user in your user database.
If either condition is true, the user has already signed upwardly and yous can issue an access token.
If neither the Google Business relationship ID nor the electronic mail accost specified in the assertion matches a user in your database, the user hasn't signed upwardly nonetheless. In this case, your token exchange endpoint should reply with a HTTP 401 error, that specifies mistake=user_not_found, as in the following example:
HTTP/1.1 401 Unauthorized Content-Type: application/json;charset=UTF-8 { "fault":"user_not_found", } When Google receives the 401 error response with a user_not_found error, Google calls your token exchange endpoint with the value of the intent parameter set to create and sending an ID token that contains the user's profile information with the request.
Handle account cosmos via Google Sign-In
When a user needs to create an account on your service, Google makes a request to your token exchange endpoint that specifies intent=create, every bit in the post-obit example:
POST /token HTTP/one.1 Host: oauth2.example.com Content-Type: awarding/x-www-class-urlencoded response_type=token&grant_type=urn:ietf:params:oauth:grant-type:jwt-bearer&scope=SCOPES&intent=create&consent_code=CONSENT_CODE&assertion=JWT[&NEW_ACCOUNT_INFO]
The exclamation parameter contains A JSON Spider web Token (JWT) that provides a signed exclamation of the Google user's identity. The JWT contains information that includes the user'south Google Account ID, name, and email address, which you can use to create a new business relationship on your service.
To answer to business relationship cosmos requests, your token exchange endpoint must exercise the following:
Validate and decode the JWT assertion
Yous can validate and decode the JWT assertion by using a JWT-decoding library for your language. Use Google'southward public keys (available in JWK or PEM format) to verify the token's signature.
When decoded, the JWT assertion looks similar the following example:
{ "sub": 1234567890, // The unique ID of the user'due south Google Account "iss": "https://accounts.google.com", // The assertion'south issuer "aud": "123-abc.apps.googleusercontent.com", // Your server's client ID "iat": 233366400, // Unix timestamp of the assertion's cosmos time "exp": 233370000, // Unix timestamp of the assertion's expiration time "proper name": "January Jansen", "given_name": "Jan", "family_name": "Jansen", "email": "jan@gmail.com", // If nowadays, the user's email address "locale": "en_US" } In addition to verifying the token's signature, verify that the assertion'due south issuer (iss field) is https://accounts.google.com and that the audience (aud field) is the client ID assigned to your Activeness.
Validate user data and create new business relationship
Check whether either of the following conditions are truthful:
- The Google Business relationship ID, establish in the exclamation's
subfield, is in your user database. - The email address in the exclamation matches a user in your user database.
If either status is truthful, prompt the user to link their existing business relationship with their Google Business relationship by responding to the request with an HTTP 401 error, specifying error=linking_error and the user's email address as the login_hint, as in the following case:
HTTP/1.1 401 Unauthorized Content-Type: application/json;charset=UTF-8 { "error":"linking_error", "login_hint":"foo@bar.com" } If neither condition is true, create a new user account using the information provided in the JWT. New accounts do non typically have a countersign set up. It is recommended that yous add together Google Sign In to other platforms to enable users to log in via Google across the surfaces of your application. Alternatively, you tin can email the user a link that starts your password recovery flow to allow the user to set a password for signing in on other platforms.
When the creation is completed, issue an admission token and render the values in a JSON object in the body of your HTTPS response, like in the following example:
{ "token_type": "Bearer", "access_token": "ACCESS_TOKEN", "expires_in": SECONDS_TO_EXPIRATION } Design the voice user interface for the authentication catamenia
Cheque if the user is verified and first the account linking catamenia
- Open your Deportment Builder project in the Actions Panel.
- Create a new scene to beginning account linking in your Action:
- Click Scenes.
- Click the add (+) icon to add a new scene.
- In the newly created scene, click the add together icon for Atmospheric condition.
- Add a condition that checks if the user associated with the conversation is a a verified user. If the cheque fails, your Action can't perform account linking during the conversation, and should fall back to providing access to functionality that doesn't require account linking.
- In the
Enter new expressionfield under Condition, enter the following logic:user.verificationStatus != "VERIFIED" - Under Transition, select a scene that doesn't crave account linking or a scene that is the entry point to guest-just functionality.
- In the
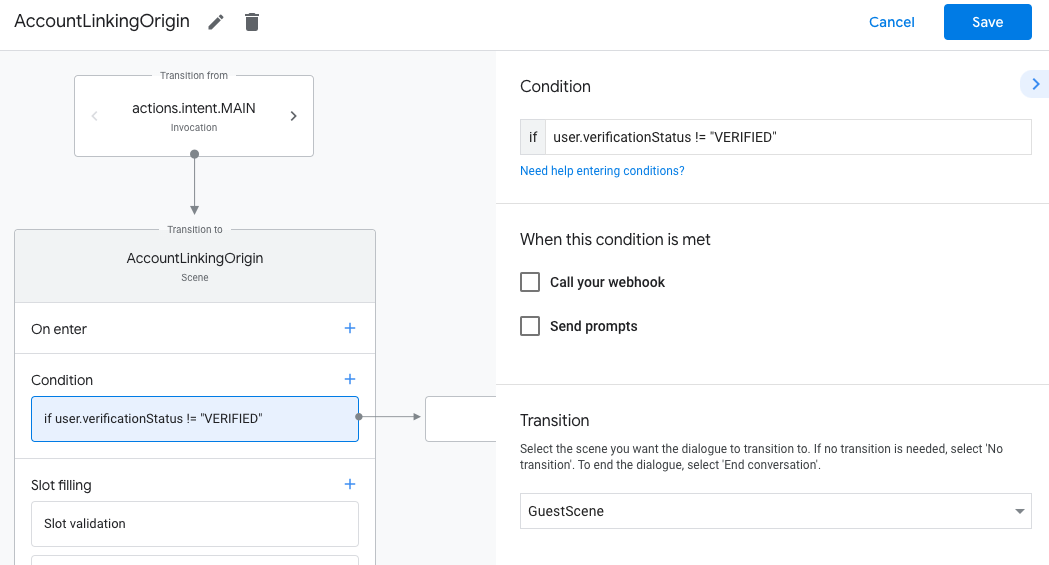
- Click the add icon for Weather condition.
- Add together a condition to trigger an account linking flow if the user doesn't have an associated identity.
- In the
Enter new expressionfield under Status, enter the following logic::user.verificationStatus == "VERIFIED" - Under Transition, select the Account Linking system scene.
- Click Save.
- In the

After saving, a new business relationship linking organisation scene called <SceneName>_AccountLinking is added to your project.
Customize the business relationship linking scene
- Under Scenes, select the account linking organisation scene.
- Click Send prompt and add a brusk judgement to draw to the user why the Activeness needs to admission their identity (for case "To save your preferences").
- Click Salvage.
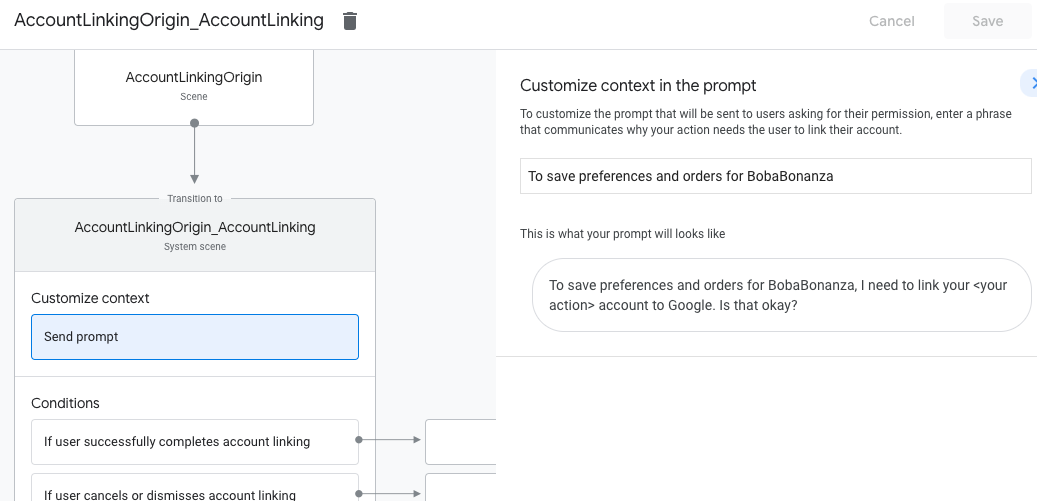
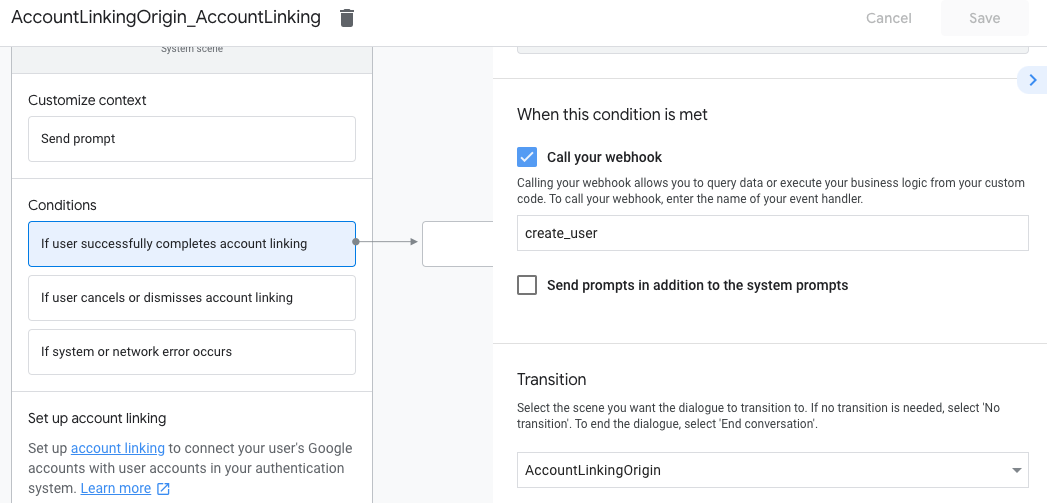
- Under Atmospheric condition, click If user successfully completes account linking.
- Configure how the flow should proceed if the user agrees to link their account. For example, telephone call the webhook to procedure whatsoever custom business logic required and transition back to the originating scene.
- Click Save.
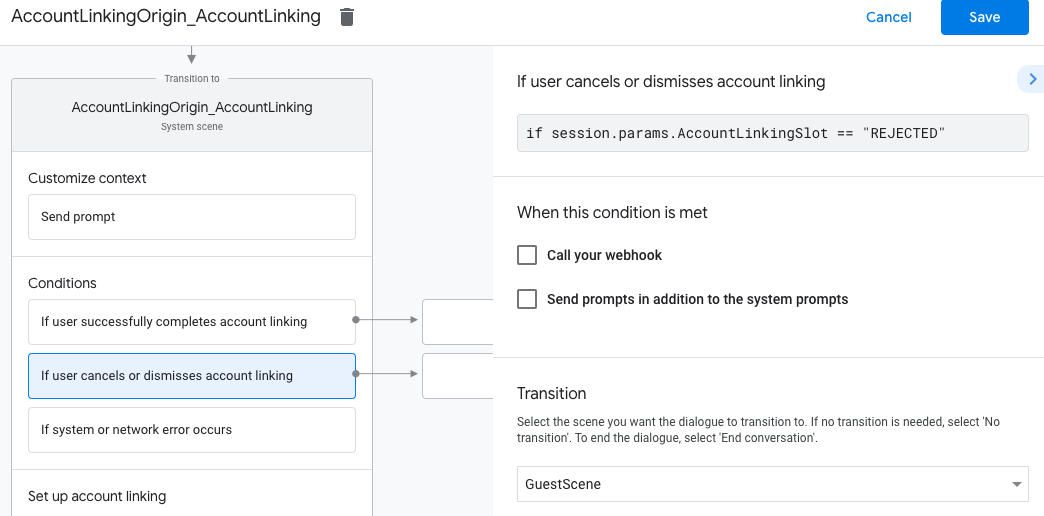
- Under Weather condition, click If user cancels or dismisses business relationship linking.
- Configure how the flow should proceed if the user doesn't agree to link their account. For instance, transport an acknowledging message and redirect to scenes that provide functionality that doesn't require business relationship linking.
- Click Save.
- Under Atmospheric condition, click If system or network error occurs.
- Configure how the catamenia should proceed if the business relationship linking menstruation can't be completed because of arrangement or network errors. For example, send an acknowledging message and redirect to scenes that provide functionality that doesn't crave account linking.
- Click Salve.
Handle data access requests
If the Banana asking contains an access token, check kickoff that the access token is valid and non expired and then recall from your user account database the user account associated with the token.
Source: https://developers.google.com/assistant/identity/google-sign-in-oauth
0 Response to "Invalid Oauth State Please Try Again"
Post a Comment